IAM Policies and Bucket Policies and ACLs! Oh, My! (Controlling Access to S3 Resources) | AWS Security Blog
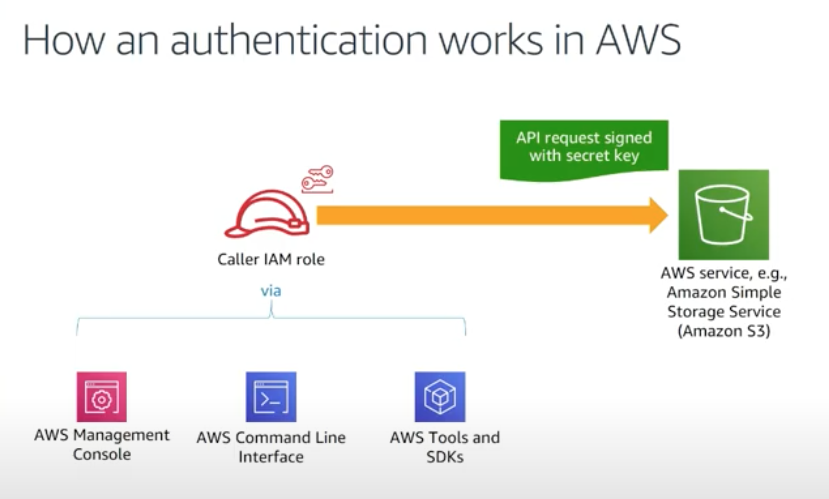
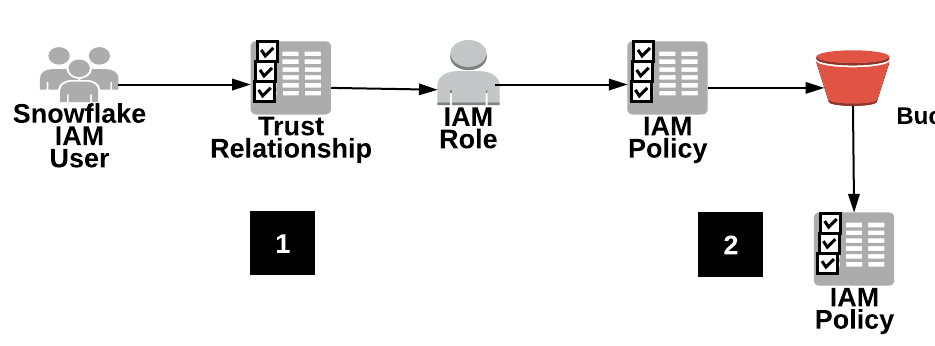
AWS Identity and Access Management (IAM) Policies, sts AssumeRole, and delegate access across AWS accounts - 2021

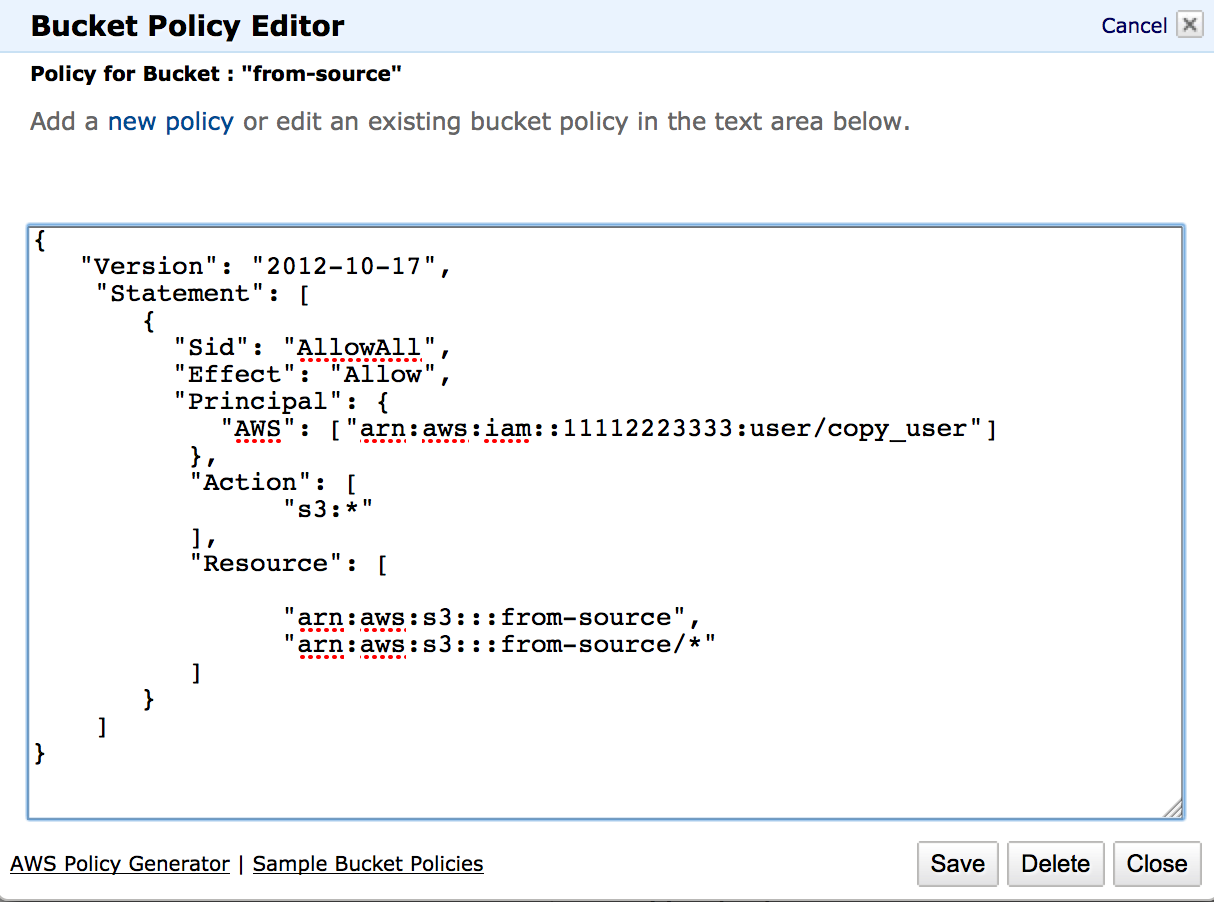
Deny All” AWS S3 Bucket Policy. How to create an AWS S3 Bucket Policy… | by Quinn Vissak | Level Up Coding

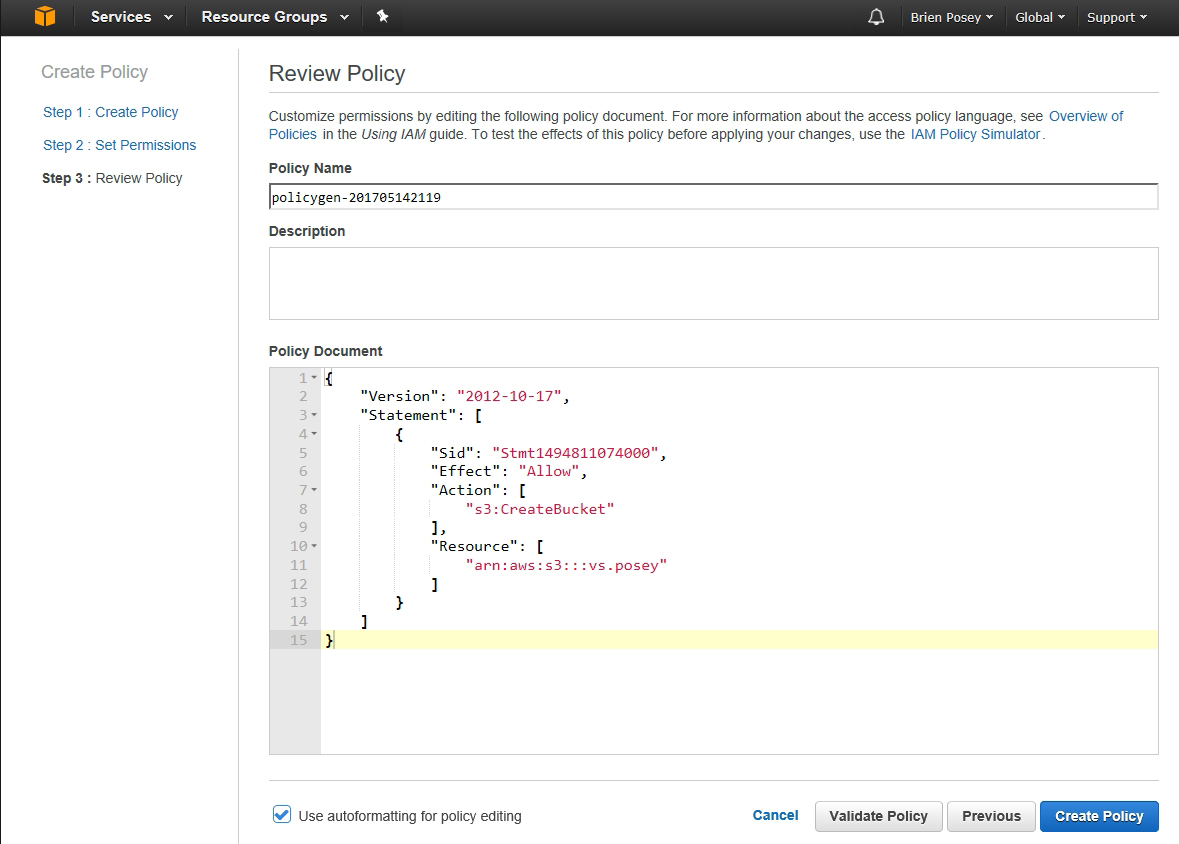
How to Use Bucket Policies and Apply Defense-in-Depth to Help Secure Your Amazon S3 Data | AWS Security Blog
How to scale your authorization needs by using attribute-based access control with S3 | AWS Security Blog